TL;DR:
- Verifying interview legitimacy is crucial to avoid scams; check email domains and official company channels.
- Preparation involves structured storytelling frameworks like STAR and SOAR for behavioral responses.
- Using AI tools as a structural aid enhances performance once the interview process is confirmed as genuine.
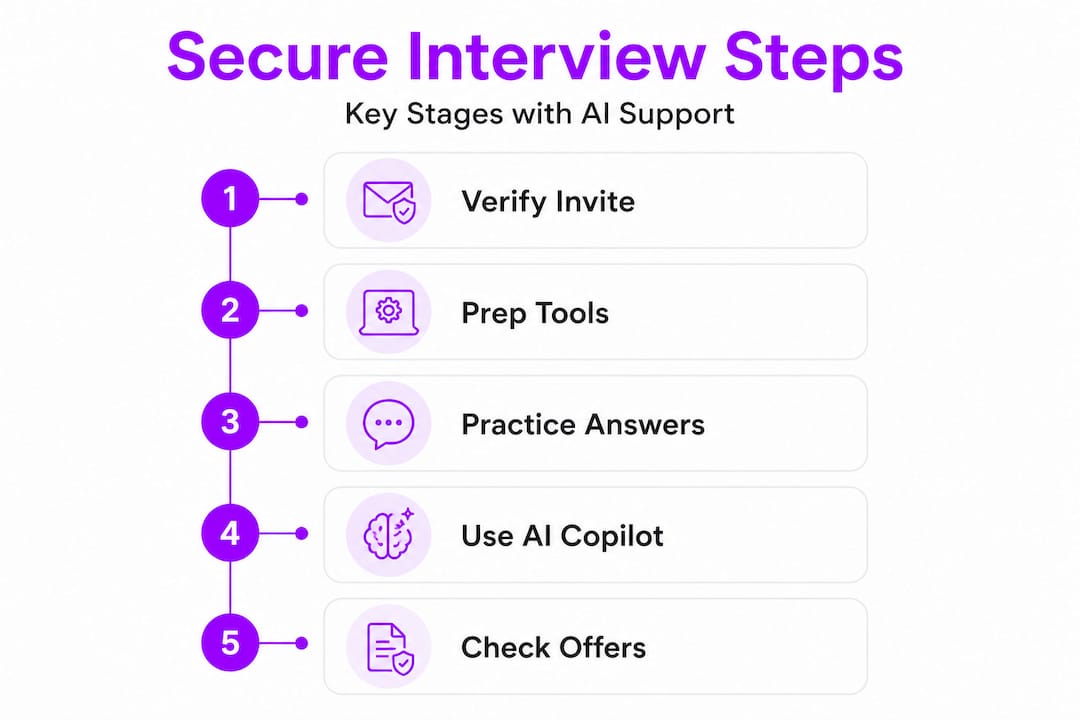
Landing a job offer takes more than rehearsing answers. Every stage of the interview process carries real risks, from fake recruiter scams designed to steal your personal data to the very human problem of losing your train of thought under pressure. Most prep guides treat those two problems separately, but they are deeply connected. If you don’t verify the process first, no amount of polished answers will protect you. This guide walks you through a complete, step-by-step approach to securing your interview from the first recruiter message to the final offer letter, with practical frameworks and smart AI tools reinforcing every stage.
Table of Contents
- What you need before you start: Tools and security essentials
- Step-by-step secure preparation: Technical and behavioral rounds
- Real-time interview execution: Security, communication, and AI copilots
- Final verification: Vet offers, follow up, and stay protected
- The truth most guides miss about securing your interview process
- Take control: Level up your interview process with MeetAssist
- Frequently asked questions
Key Takeaways
| Point | Details |
|---|---|
| Verify before you share | Always confirm recruiter legitimacy and scheduling before sharing any sensitive data. |
| Structure beats nerves | Use frameworks like STAR and SOAR to organize responses and minimize stress. |
| AI is a supplement | AI copilots anchor your answers but cannot replace practice or genuine understanding. |
| Clarify constraints up front | Always clarify interview questions before diving into solutions, especially in technical rounds. |
| Stay vigilant post-interview | Continue verifying offers and refuse any requests for payment or personal data after your interview. |
What you need before you start: Tools and security essentials
Now that you understand the stakes, let’s lay the foundation for a secure and productive interview process. Before you open a single coding editor or rehearse a single story, you need to confirm that the opportunity in front of you is actually real.
Fake interview scams have grown more sophisticated in recent years. Fraudsters now mirror real company branding, use convincing LinkedIn profiles, and request sensitive documents under the guise of background checks. The first line of defense is a deliberate verification routine, not trust based on a polished email.
A solid verification roadmap means pausing before responding, documenting every piece of outreach you receive, verifying the recruiter’s identity through the company’s official website or LinkedIn, requesting that all scheduling happen through official platforms, and refusing any early requests for money, ID photos, or banking details. These steps sound obvious, but candidates under excitement or financial pressure regularly skip them.
Here is a pre-interview security checklist to run through before accepting any interview request:
- Confirm the recruiter’s email domain matches the company’s official website exactly
- Search the recruiter’s name on the company’s official LinkedIn page
- Request a calendar invite from a verified company email address
- Use a dedicated professional email address for job applications (not your personal account)
- Store all recruiter communications in a labeled folder with timestamps
- Review interview privacy best practices before sharing any documents
- Follow proven technical interview prep steps only after you confirm the opportunity is legitimate
On the tools side, you need a stable internet connection, a computer with a tested microphone and camera, a browser with only trusted extensions active, and a reliable AI copilot if you plan to use one. Protecting sensitive data during the prep phase means being selective about which platforms you share your resume with and ensuring any AI tool you use encrypts your data.
| Security check | What to verify | Red flag |
|---|---|---|
| Email domain | Matches official company site | Free email (Gmail, Yahoo) |
| Recruiter identity | Listed on company LinkedIn | No profile or very new account |
| Scheduling method | Official platform or company calendar | WhatsApp, text only |
| Document requests | Only after confirmed offer stage | ID or banking info upfront |
| Payment | Never required | Any fee request |
Pro Tip: Set up a free dedicated email address just for job applications. It makes it easier to track outreach, spot impersonators, and keep your personal inbox clean. Record your verification steps in a simple spreadsheet.
Step-by-step secure preparation: Technical and behavioral rounds
With your foundation in place, it’s time to structure your practice and responses effectively for each interview round. Technical and behavioral interviews require different preparation strategies, but they share one critical principle: eliminate ambiguity before it eliminates you.
For technical rounds, a step-by-step structure means first identifying the tools and skills required for the role, then checking relevant resources and practicing, then preparing questions to ask your interviewer, and finally planning your time and materials ahead of the session. For coding roles specifically, this means practicing thinking out loud while solving problems and using clarifying questions to prevent misunderstandings about constraints or edge cases.
Here is a numbered preparation checklist you can apply per round:
- Identify the specific interview format (coding, system design, behavioral, take-home)
- List the required tools and make sure they are installed and tested
- Review the job description and map skills to practice topics
- Practice at least two coding problems per day using a timer
- Prepare three behavioral stories and rehearse them out loud
- Write down five questions to ask the interviewer
- Confirm your internet speed and video setup the evening before
- Review your resume and any documents you submitted
For behavioral rounds, structured storytelling frameworks like STAR and SOAR are repeatedly recommended for organizing answers under pressure. Practicing them out loud (not just mentally) forces you to notice where your story loses clarity.
Here is how STAR and SOAR compare:
| Framework | Stands for | Best used for | Key strength |
|---|---|---|---|
| STAR | Situation, Task, Action, Result | Behavioral questions with clear outcomes | Simple structure, widely recognized |
| SOAR | Situation, Obstacle, Action, Result | Stories involving specific challenges overcome | Highlights problem-solving ability |
Both frameworks help when you are nervous and your memory goes blank. Having your STAR and SOAR frameworks pre-mapped to specific stories means you don’t have to construct a narrative under real-time pressure. You simply recall and deliver.
For coding interviews specifically, check out these behavioral interview tips for developers to see how you can adapt behavioral prep for technical roles where communication matters just as much as code.
You also want to be careful about digital security for candidates during your prep phase. Avoid storing sensitive personal details in public cloud documents and use password-protected files when sharing resumes on new platforms.
Safety note: Always clarify the question’s constraints before starting your solution. Jumping straight into code without confirming input types, edge cases, or expected outputs is one of the fastest ways to fail a technical round.
Pro Tip: Practice your behavioral stories out loud, on camera, at least once. Watching yourself back reveals filler words, weak transitions, and moments where your story loses structure. Aim to have at least three solid stories ready that can flex across multiple question types.
Real-time interview execution: Security, communication, and AI copilots
Once you’re ready to perform, let’s focus on secure, high-performance interview execution and how modern AI tools can help under pressure.

The moment your interview begins, two things must stay true: your data hygiene must be solid and your communication must be clear. Those two goals support each other. When you are confident about your environment, you free up mental bandwidth for actual performance.
Here is a quick reference for in-interview data hygiene:
- Keep only official or trusted browser tabs open during the session
- Mute your microphone when you are not speaking to reduce background noise and accidental sharing
- Confirm the interviewer’s identity at the start if you have any uncertainty
- Take brief notes on a physical notepad rather than a third-party app during sensitive stages
- Do not paste personal information into any chat function without verifying the platform
- Close unrelated browser tabs before screen sharing begins
On the performance side, AI for coding challenges works best as a structural layer rather than a replacement for genuine understanding. Think of it like a scaffold on a building under construction. It holds the structure in place while you do the real work. Once the work is done, you remove it and what remains should stand on its own.
AI copilot tools are best treated as a supplemental structure layer to maintain your answer outline under pressure, not as a substitute for genuine understanding. If you haven’t practiced offline, no AI tool will save you when a follow-up question goes off-script.
One of the most common failure points in technical interviews is misunderstood constraints. Practicing thinking out loud and using clarifying questions before starting your solution dramatically reduces the chance of solving the wrong problem. This matters even more when you are using screen-sharing tools, since your interviewer can see exactly when you start typing, and starting too fast signals a lack of methodical thinking.
Understanding the types of technical interviews you might face, from live coding sessions to asynchronous take-homes, also helps you decide how and when to use an AI copilot appropriately.
MeetAssist’s Phone Mode is particularly useful here. By moving all AI suggestions to your phone screen after scanning a QR code, nothing extra is visible on your computer during screen-sharing sessions. You get real-time structure prompts without any visible extension on screen, which keeps your workspace clean and your focus intact.
Pro Tip: Treat your AI copilot as a confidence checkpoint, not a crutch. Use it heavily in offline practice to sharpen your structure, then rely on your own memory and pacing during the actual session.
Final verification: Vet offers, follow up, and stay protected
After you’ve given your best in the interview, ensure you don’t fall victim to scams or data leaks by carefully managing the post-interview phase.
The period between finishing an interview and accepting an offer is surprisingly high-risk. Scammers often target candidates at this stage by sending fake offer letters with requests to complete onboarding forms that capture sensitive data. Excitement makes people lower their guard, which is exactly what fraudsters count on.
A secure post-interview routine looks like this:
- Send a follow-up thank-you email to the interviewer using the same verified email thread from earlier
- Wait for communications only from the confirmed company domain
- Verify the offer letter against the company’s official documentation format
- Research the company’s real address, phone number, and legal entity name before proceeding
- Request any sensitive onboarding forms only through official HR platforms or portals
- Cross-reference any verbal commitments against written documentation before signing
- Consult a trusted contact or employment advisor if anything feels off
Evaluating digital security during the offer stage means being just as cautious as you were at the start. Some fake job scams are designed specifically to reach the offer stage before requesting data, because that is when candidates feel the most committed and least likely to question the process.
The same verification roadmap that applies at the beginning applies here too: pause, document, verify through official channels, request official scheduling, and refuse any early requests for sensitive data or payment.
Warning: No legitimate employer will ever ask you to pay money, send gift cards, or share banking information as part of the interview or onboarding process. If that request appears, stop communicating immediately.
Pro Tip: Keep a log of every message, email, and call related to your job search in a simple spreadsheet. Include the date, platform, name of the contact, and a summary of what was discussed. This takes five minutes and becomes invaluable if you need to dispute anything later.
The truth most guides miss about securing your interview process
Most interview guides split into two camps. One side focuses entirely on how to answer questions well. The other focuses on how to avoid scams. Very few people talk about how these two concerns are actually the same problem, because both come down to eliminating ambiguity and staying in control.
Think about what a scam and a botched technical answer have in common. In both cases, you moved forward before you fully understood what was in front of you. With a scam, you shared information before verifying legitimacy. With a botched answer, you started solving before clarifying the constraints. The root behavior is identical: acting before verifying.
That is why combining proven technical interview prep with genuine security habits produces better outcomes than either approach alone. When you develop the discipline to pause and verify before acting, that same discipline shows up in how you handle coding problems, how you structure behavioral answers, and how you respond to unexpected follow-up questions.
The concern with over-reliance on any AI tool, or any security checklist for that matter, is that it creates a false sense of control. A candidate who depends entirely on an AI copilot for structure will fall apart the moment the tool lags or the question goes off-script. A candidate who follows a security checklist mechanically but doesn’t actually understand what they are looking for will still miss sophisticated scams.
Real coding interview prep strategies treat AI as a scaffolding tool, not a safety net. You build real understanding first, then use AI to strengthen delivery. Verifying legitimacy works the same way. You develop actual judgment about what feels right, then use a checklist to confirm that judgment.
The contrasting view worth internalizing here is that security-focused guidance for job seekers and performance-focused AI tools are serving different moments in the same journey. Step one is always to verify that the process is legitimate. Step two is to use AI strictly to improve your delivery and structure once that legitimacy is confirmed. Skipping step one and jumping to step two is how candidates get burned on both fronts.
The most prepared candidate in any room isn’t the one who memorized the most answers. It’s the one who built habits around clarity, verification, and controlled performance, and used tools to reinforce those habits rather than replace them.
Take control: Level up your interview process with MeetAssist
Equipped with actionable strategies, it’s time to boost your readiness with tools that protect your time and elevate your performance.
If you’ve worked through this guide and want a practical way to apply everything you’ve learned, MeetAssist was built exactly for this moment.
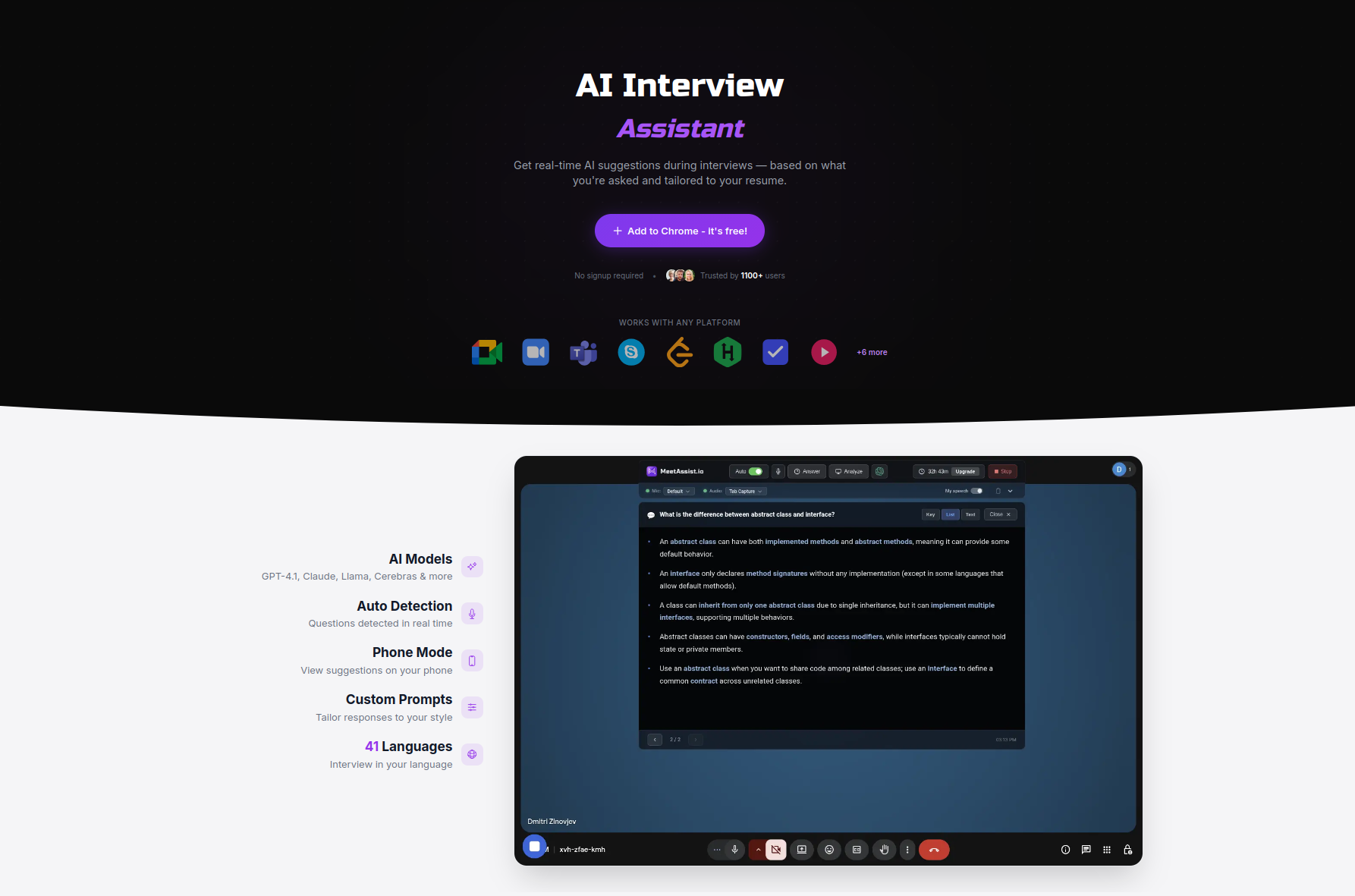
MeetAssist is a Chrome extension that listens to your interview in real time and surfaces structured AI-powered suggestions directly on your screen, or via Phone Mode, entirely on your phone so nothing appears on your computer during screen-sharing. It supports multiple AI models including GPT-4.1, Claude, and Llama, with customizable answer styles like STAR, bullet points, or concise responses. You can upload your resume for personalized answers, and no audio or video is ever recorded. Explore AI assistant alternatives to see how MeetAssist compares, or go straight to the AI coding interview assistant to start practicing your technical rounds today. Pricing is a one-time purchase with no subscription required.
Frequently asked questions
How do I verify if an interview invite is legitimate?
Always check that the sender’s email domain exactly matches the company’s official website, and request official scheduling through the company’s platform before sharing any personal information.
What are the best frameworks for structuring interview answers?
Use STAR or SOAR to organize your behavioral stories, and practice delivering them out loud multiple times before the actual interview.
Is it safe to use AI tools during technical interviews?
AI tools help you stay organized and reduce nerves, but they work best as a structural supplement after you’ve confirmed the interview process is legitimate and built solid foundational knowledge.
How do I avoid common mistakes in technical interview prep?
Always clarify the problem’s constraints before writing any code, practice thinking out loud, and use structured frameworks to organize your responses from the start.
What should I do if an interviewer requests money or sensitive info?
Stop the conversation immediately and refuse. No legitimate interview process requires payment, gift cards, or banking information at any stage.
Recommended
- Maintain interview privacy: Best practices for remote job seekers | MeetAssist
- Confident Interview Preparation Steps for Technical Success – MeetAssist | MeetAssist
- How to use AI in interviews for job success in 2026 | MeetAssist
- AI interview privacy: what job seekers need to know | MeetAssist
- Checklist za AI inovacije: vodič za prodajne ekipe - ChatTrips




